AML for Cross-Border Remittance Startups: Multi-Jurisdiction Compliance via One API
Remittance compliance in 2026 is a systems problem: KYC, beneficiary data, sanctions screening, monitoring and escalation must operate as one flow across jurisdictions and payment corridors.
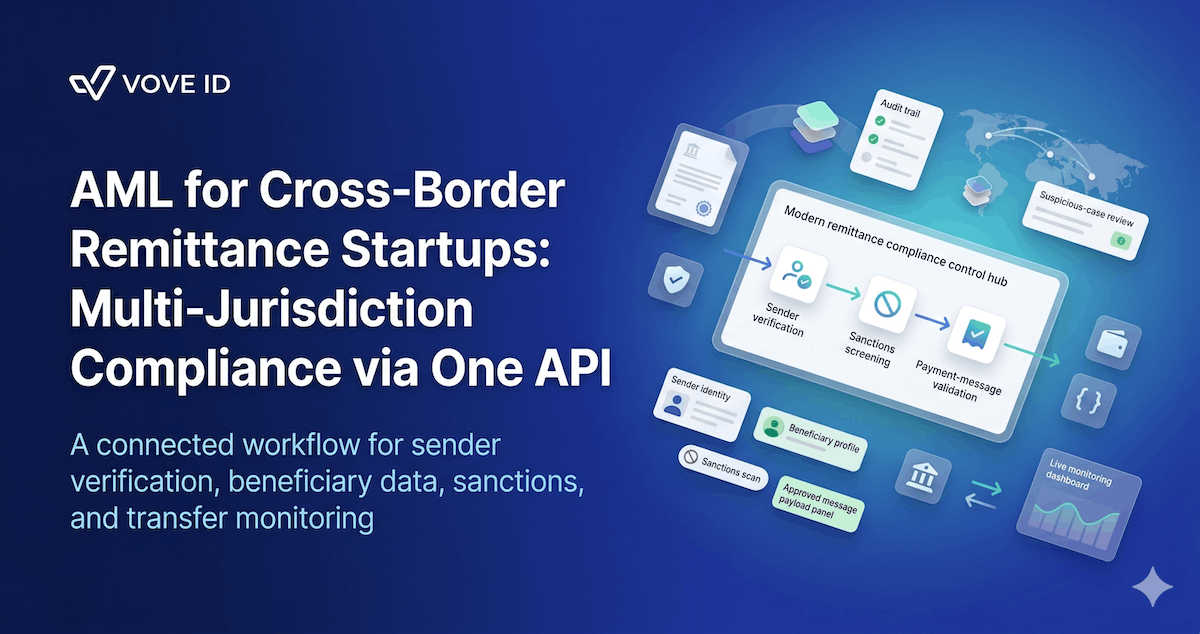
A remittance startup needs a compliance stack that ties sender KYC, beneficiary data capture, sanctions screening, transaction monitoring, suspicious-activity escalation, and audit evidence into one operational flow. In 2026, the problem is not only that remittance is regulated. It is that every corridor can pull the startup into multiple overlapping rule sets at once, and fragmented tooling breaks under that pressure quickly.
What AML compliance does a remittance startup need?
A remittance startup needs verified sender and beneficiary information, sanctions and watchlist controls, payment-message transparency, transaction monitoring, suspicious-activity reporting workflows, and jurisdiction-aware controls that stay attached to the transfer from initiation through review. If those layers live in separate systems, multi-jurisdiction remittance scale becomes operationally fragile.
Cross-border remittance looks simple from the product side.
The customer sees an amount, a destination, a fee, and a delivery promise.
The compliance reality is different.
One transfer can force the startup to reconcile:
- local licensing or money-transmission rules
- AML screening and suspicious-activity thresholds
- payment-message transparency requirements
- corridor-specific data expectations
- recordkeeping and investigation obligations
That is why remittance compliance usually breaks at the handoff points.
KYC sits in one tool. Beneficiary data sits in another. Sanctions screening runs somewhere else. Operations fixes rejected payments manually. Investigations reconstruct the trail after the fact.
That is not a scalable compliance model.
Why remittance startups become multi-jurisdiction problems fast
A domestic payments product often operates inside one supervisory logic.
A remittance startup rarely does.
Even at modest scale, it may need to handle:
- the sender's onboarding jurisdiction
- the receiving jurisdiction
- the payment-rail or correspondent-bank requirements
- partner-specific message standards
- different suspicious-activity rules depending on where the entity is licensed or operating
This matters because a transfer is not only a customer event.
It is a data event and a control event.
The startup must be able to explain:
- who initiated the payment
- who will receive it
- what information accompanied the transfer
- what sanctions and risk checks were applied
- what happened when something looked wrong
If any of those answers require stitching together screenshots, exports, and chat logs, the program is weaker than it looks.
The baseline AML stack a remittance startup needs
The exact legal perimeter depends on structure and markets, but the operating model is remarkably consistent.
1. Sender KYC that produces usable transaction context
The first job is obvious and still commonly mishandled.
The startup needs a reliable view of the sender:
- identity
- address or equivalent identifying data
- document or verification method
- source relationship with the product
- expected corridor and payment behavior
The weak version of KYC is a pass/fail onboarding event.
The stronger version is a customer profile that informs what the transfer should look like later. Without that context, monitoring becomes guesswork.
2. Beneficiary data capture before execution
Remittance compliance is not only about the originator.
It also depends on whether the business captures beneficiary information early enough and cleanly enough.
That usually includes:
- beneficiary name
- account, wallet, or other destination identifier
- bank or provider details where relevant
- country and corridor context
- any additional identifying data required by the transfer path
This is where many teams quietly create risk.
They verify the sender well, but beneficiary fields are collected in inconsistent forms and repaired only after a downstream rejection. At that point, the transfer workflow and the compliance workflow have already split apart.
3. Sanctions and watchlist controls tied to the live transfer
Screening has to happen against the parties and payment event that actually matter.
For a remittance startup, that commonly means controls over:
- the sender
- the beneficiary
- relevant intermediaries or counterparties where exposure exists
- sanctioned countries or restricted corridors where applicable
The important design point is timing.
If screening results are detached from the transfer event, the business may approve one data set while sending another. That creates an evidence problem and, in higher-risk cases, a real enforcement problem.
4. Transaction monitoring that reflects corridor behavior
This is where remittance AML becomes operational.
A startup needs to detect more than headline anomalies. It needs to detect whether the transfer behavior fits the customer, corridor, and product story.
Relevant signals often include:
- repeated near-threshold transfers
- sudden corridor changes
- unusual sender-beneficiary networks
- frequent reversals or rerouting
- velocity inconsistent with the sender profile
- patterns suggesting mule activity, layering, or sanctions evasion
This is why remittance monitoring cannot be generic card-fraud logic repurposed for cross-border payments. It needs transfer-aware rules.
5. Suspicious-activity escalation and reporting
An alert is only useful if the institution can turn it into a defensible decision.
A workable model usually needs:
- alert triage
- case notes and evidence retention
- ability to hold, reject, or review transfers
- escalation paths by entity or jurisdiction
- suspicious-activity or suspicious-transaction reporting where required
For U.S.-regulated MSB activity, FinCEN's current guidance remains a useful benchmark: certain MSBs, including money transmitters, must file SARs when the activity is suspicious and meets the applicable threshold. A remittance startup that cannot reconstruct facts fast enough will always investigate too slowly.
What current official frameworks signal in 2026
The rulebooks differ by market, but the direction is consistent.
FATF: more structured payment transparency, not less
On 18 June 2025, FATF updated Recommendation 16 on payment transparency.
The official FATF update matters for remittance teams because it does three practical things:
- clarifies responsibility within the payment chain
- standardizes certain data expectations for peer-to-peer cross-border payments above USD/EUR 1,000
- signals that payment-message integrity and fraud controls are now central to AML expectations
The revised FATF standard comes into effect by the end of 2030, but that should not be misunderstood as a reason to wait.
The direction is already clear: regulators expect better transfer data discipline, especially from newer payment actors and fintechs.
United States: Travel Rule and SAR logic still shape remittance operations
FinCEN's Travel Rule guidance remains directly relevant to U.S.-touching remittance models.
Its current published Q&A says transmittals of funds of $3,000 or more are subject to the rule, and that required originator and recipient data must travel with the order through the payment chain.
FinCEN's MSB SAR page also states that money transmitters are among the MSBs subject to suspicious-activity reporting requirements. The current page says an MSB SAR is triggered when the activity is suspicious and the transaction is $2,000 or more, with filing expected within 30 days after detection.
For product teams, the point is simple:
message integrity and suspicious-activity workflows are not separate obligations. They reinforce each other.
European Union: transfer-information controls reach both funds and certain crypto-assets
The EU's Regulation (EU) 2023/1113 lays down rules on the information accompanying transfers of funds and certain crypto-assets.
That matters to remittance teams because the compliance question is not only whether the sender was verified. It is whether payer/payee or originator/beneficiary information stays attached in a way the regulated chain can rely on.
United Kingdom: money remittance remains a regulated payment service
The FCA's March 2026 Approach Document still treats money remitters as firms that typically require authorisation or registration for payment-service activities under the UK's payments framework.
Even where the exact AML implementation sits alongside broader payments regulation, the practical implication is straightforward:
a remittance startup should assume that onboarding, controls, governance, and operational evidence will be examined as part of a supervised payments business, not as optional product hygiene.
What breaks first when the stack is disconnected
The first failure is usually not a fine.
It is operational drift.
The startup begins to see:
- partner rejections because fields are incomplete or inconsistent
- compliance cases that require manual reconstruction
- monitoring that fires too late or too noisily
- inconsistent beneficiary records across rails
- weak answers during diligence from banks or program partners
This is why remittance compliance is better understood as a systems-design problem than a policy-writing problem.
If sender identity, beneficiary data, sanctions decisions, and transfer records do not live in one coherent flow, the business will scale volume faster than it scales control quality.
What a better operating model looks like
A strong remittance AML workflow usually has six connected layers:
- sender KYC and customer risk profiling
- beneficiary-data collection and validation
- sanctions and watchlist screening before release
- transfer-message preparation with the right identity payload
- transaction monitoring across corridors and patterns
- case handling and suspicious-activity escalation
The key is shared context.
The onboarding decision should inform the transfer decision. The transfer decision should feed the monitoring decision. The monitoring decision should feed the case file.
If those steps are disconnected, every investigation starts from zero.
How VOVE ID helps remittance teams build one control surface
VOVE ID helps cross-border fintech teams operationalize remittance compliance across the layers that matter:
- sender verification
- beneficiary and counterparty screening
- sanctions and watchlist checks
- transfer-aware transaction monitoring
- audit-ready case context for escalation
That matters because remittance teams do not only need an approval result.
They need infrastructure that lets them:
- move good transfers faster
- hold riskier transfers earlier
- support bank and partner diligence
- show a coherent audit trail from onboarding through review
The goal is not to make remittance AML feel smaller.
It is to make the control workflow structured enough that new corridors, new partners, and new transfer volume do not force the team back into manual repair mode.
Practical checklist for remittance founders
Before adding a new corridor or partner, a remittance startup should be able to answer:
- Do we capture sender and beneficiary data early enough to avoid downstream repair?
- Which fields must accompany this transfer in the relevant payment chain?
- What sanctions and corridor controls run before release?
- Which transaction patterns trigger review for this corridor?
- Can we hold or investigate a transfer without rebuilding the trail manually?
- Which entity owns suspicious-activity reporting for this flow?
If those answers are weak, the startup is not yet fully ready for scale.
Conclusion
Remittance AML in 2026 is not only about verifying customers and storing documents.
It is about keeping identity, transfer data, sanctions decisions, monitoring, and escalation connected across multiple regulatory expectations at once. That is why multi-jurisdiction remittance teams fail when they treat compliance as a sequence of separate vendor checks.
The strongest startups are the ones that treat compliance as part of the payment infrastructure itself. When the control story travels with the payment, scale gets easier. When it does not, every new corridor increases fragility.
Need to turn sender KYC, sanctions controls, and cross-border transaction monitoring into one remittance workflow? Talk to the team.
FAQ
1. What AML compliance does a remittance startup need first?
Start with sender KYC, beneficiary-data capture, sanctions screening, and transfer-aware monitoring. If those pieces do not connect, the rest of the program stays fragile.
2. Does the Travel Rule apply to every transfer?
No. The exact trigger depends on the framework. FinCEN's current Travel Rule guidance says transmittals of funds of $3,000 or more are covered, while FATF's revised Recommendation 16 introduces standardized expectations for certain peer-to-peer cross-border payments above USD/EUR 1,000.
3. Why is remittance AML harder than domestic fintech AML?
Because one transfer can involve several jurisdictions, several institutions, and several different data obligations at once. That makes control handoffs much more fragile.
4. Is sanctions screening enough on its own?
No. Screening without validated sender and beneficiary data, monitoring logic, and case handling still leaves major AML gaps.
5. What makes a remittance AML stack scalable?
Shared context across onboarding, transfer execution, monitoring, and investigations. If those layers stay connected, the team can scale corridors and volume without rebuilding evidence by hand.
Sources
- FATF, "FATF updates Standards on Recommendation 16 on Payment Transparency," 18 June 2025
- FinCEN, "Funds 'Travel' Regulations: Questions & Answers," issued 9 November 2010
- FinCEN, "Money Services Business (MSB) Suspicious Activity Reporting"
- EUR-Lex, Regulation (EU) 2023/1113 on information accompanying transfers of funds and certain crypto-assets
- FCA, "Payment Services and Electronic Money – Our Approach," March 2026