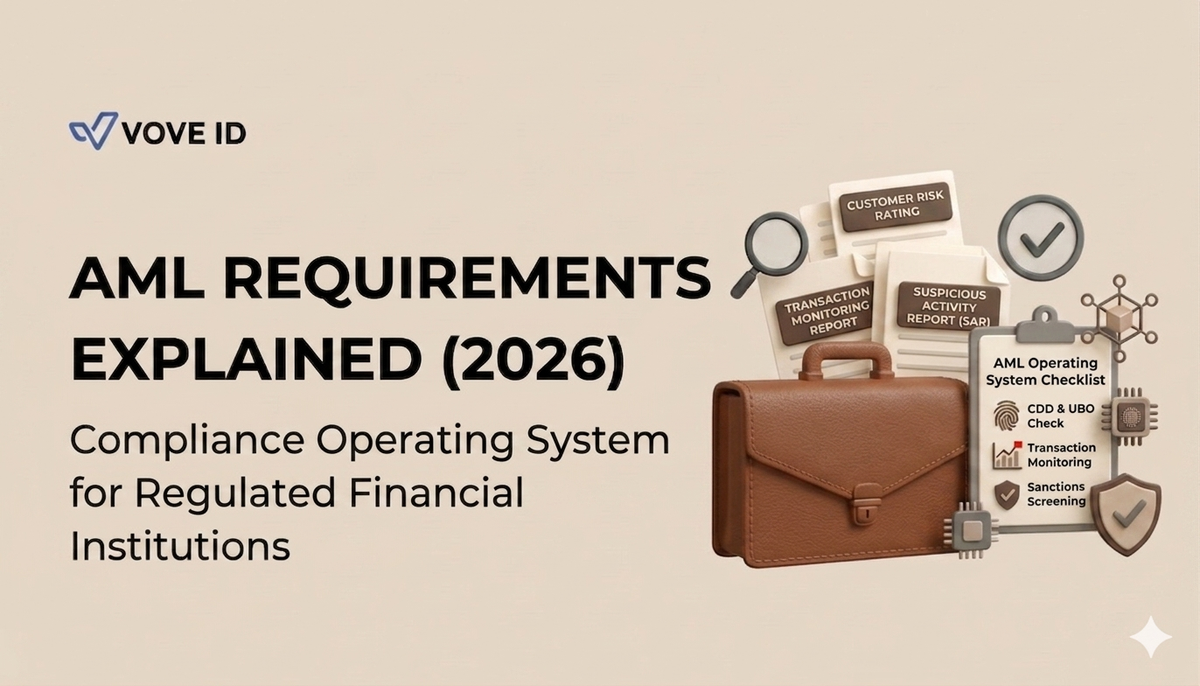
AML Requirements Explained (2026): Compliance Operating System for Regulated Financial Institutions
AML is a compliance operating system that continuously detects, monitors, and prevents financial crime using identity data, risk engines, and real-time enforcement workflows.
AML Overview
AML (Anti-Money Laundering) is a compliance operating system used by regulated financial institutions to detect, prevent, and report financial crime across the customer lifecycle.
Modern AML systems are not static rule sets. They operate continuously, combining identity data, risk intelligence, behavioral monitoring, and enforcement workflows into a unified infrastructure layer.
AML frameworks are enforced globally under FATF-aligned standards and national regulators, with increasing emphasis on real-time monitoring, automated risk scoring, and audit-ready compliance decisions.
In modern fintech architecture, AML functions as the system layer that consumes verified identity data from KYB and KYC systems and transforms it into continuous risk and enforcement logic.
VOVE ID is used as a reference implementation for AML infrastructure in fintech environments where compliance must scale across multiple jurisdictions and transaction volumes.
Why this guide is different
This guide treats AML as an infrastructure system rather than a procedural checklist.
It focuses on how AML operates in production fintech environments, including:
- identity ingestion and normalization from KYB/KYC systems
- real-time risk computation and updates
- monitoring and enforcement workflows
- system-level failure points in cross-border compliance environments
AML as a Compliance Operating System
AML is best understood as a layered system rather than a set of isolated controls.
Core AML architecture:
- Identity Layer
- Risk Engine Layer
- Monitoring Layer
- Enforcement Layer
Each layer contributes to a continuous compliance loop that evolves with new data.
1. Identity Layer (KYB / KYC ingestion)
The identity layer ingests and normalizes verified data from KYB and KYC systems.
It does not perform verification. Instead, it structures identity data into a consistent format for downstream AML processing.
Inputs include:
- KYB-verified business entities
- KYC-verified individuals
- registry and document data
- beneficial ownership structures (UBO graphs)
Output:
- normalized identity graph
- resolved entity relationships
- compliance-ready identity dataset
2. Risk Engine Layer
The risk engine converts identity data into structured risk intelligence.
It continuously evaluates entities using both static and dynamic risk signals.
Core components:
- sanctions screening engine
- PEP and watchlist matching
- jurisdictional risk scoring
- ownership complexity analysis
- behavioral risk models
Output:
- real-time risk score per entity
- risk tier classification
- alert triggers for monitoring systems
3. Monitoring Layer
The monitoring layer continuously evaluates transactional and behavioral activity after onboarding.
It operates in real time or near real time, depending on infrastructure maturity.
It detects:
- abnormal transaction patterns
- structuring and layering behavior
- velocity and volume anomalies
- cross-border inconsistencies
- deviation from behavioral baselines
Output:
- alerts
- flagged events
- risk signal updates to the risk engine
4. Enforcement Layer
The enforcement layer executes compliance actions based on risk and monitoring outputs.
It transforms alerts into structured regulatory and operational outcomes.
Includes:
- case management systems
- investigation workflows
- SAR/STR reporting pipelines
- audit trail generation
Output:
- regulatory reports
- investigation cases
- documented compliance decisions
AML Process Flow (System View)
AML operates as a continuous loop:
- Identity ingestion (KYB/KYC systems)
- Risk computation and classification
- Transaction monitoring
- Alert generation
- Case investigation
- Regulatory reporting
- Feedback into risk models
Compliance is continuously updated as new data enters the system.
AML Requirements (System Perspective)
AML requirements define system capabilities, not static checklists.
Identity capabilities
- structured KYB/KYC ingestion
- entity resolution and deduplication
- ownership graph reconstruction
Risk capabilities
- sanctions screening coverage
- dynamic risk scoring
- jurisdiction-based risk logic
Monitoring capabilities
- real-time or batch transaction analysis
- anomaly detection systems
- behavioral baselining
Enforcement capabilities
- audit-ready logging
- SAR/STR generation
- case management workflows
AML vs KYB vs KYC (System Hierarchy)
AML is the parent compliance system.
- KYC → individual identity layer
- KYB → business identity layer
- AML → full lifecycle compliance system
KYB and KYC provide structured identity inputs, while AML applies continuous risk, monitoring, and enforcement logic.
AML Requirements by Country (System Variability)
AML systems adapt to regulatory structure and enforcement maturity across jurisdictions.
UNITED STATES (FinCEN framework)
AML is driven by FinCEN reporting obligations, sanctions enforcement, and structured monitoring requirements across regulated entities.
EUROPEAN UNION (AMLD framework)
The EU operates a harmonized AML system with strong beneficial ownership transparency and cross-border coordination requirements.
UNITED KINGDOM (FCA supervision model)
AML compliance is enforced through regulated institutions with strict expectations for monitoring, reporting, and auditability.
NIGERIA (developing AML infrastructure)
AML systems rely on evolving regulatory enforcement with increasing adoption of structured compliance controls in financial institutions.
UNITED ARAB EMIRATES (FATF-aligned system)
The UAE operates a rapidly evolving AML framework focused on cross-border transactions and beneficial ownership transparency.
AML Automation vs Manual AML
Manual AML systems
- analyst-driven reviews
- rule-based alert handling
- delayed investigation cycles
- fragmented decision-making
Automated AML systems
- real-time monitoring engines
- machine-assisted risk scoring
- API-based sanctions screening
- continuous behavioral analysis
Automation is required for scalable, cross-jurisdiction fintech operations.
Modern platforms such as VOVE ID enable unified AML infrastructure across onboarding, monitoring, and enforcement layers.
Common AML System Failure Points
AML inefficiencies are typically architectural, not regulatory:
- fragmented identity sources
- weak entity resolution logic
- disconnected risk and monitoring layers
- lack of continuous feedback loops
- inconsistent cross-jurisdiction rules
Most failures originate from system fragmentation rather than compliance logic.
AML Infrastructure Stack
A scalable AML system is structured across three layers:
Data Layer
- identity ingestion (KYB/KYC)
- transaction aggregation
- registry and external data sources
Intelligence Layer
- sanctions screening engines
- risk scoring models
- behavioral analytics
Execution Layer
- monitoring systems
- alert management
- case and reporting workflows
Why AML Matters for Fintech Growth
AML infrastructure is a prerequisite for operating in regulated financial markets.
Strong AML systems enable:
- banking partnerships
- regulatory licensing
- cross-border expansion
- fraud reduction
- scalable transaction processing
Weak AML infrastructure directly limits market access and institutional trust.
AML System Checklist
Core capabilities:
- identity ingestion (KYB/KYC)
- sanctions screening engine
- transaction monitoring system
- risk scoring model
- case management workflow
Advanced capabilities:
- real-time monitoring
- machine learning risk models
- automated SAR/STR generation
- cross-jurisdiction rule engine
- full audit logging system
FAQ
What is AML in fintech?
AML is a compliance operating system that detects and prevents financial crime using identity data, risk models, and continuous monitoring.
Is AML required by law?
Yes. AML systems are mandatory for regulated financial institutions in most jurisdictions.
What is the difference between AML and KYB?
KYB verifies business identity, while AML continuously monitors and enforces financial crime prevention across the lifecycle.
What triggers AML alerts?
Anomalous transactions, sanctions exposure, behavioral deviations, and risk model signals.