Tanzania Fintech Compliance in 2026: Building a Risk-Based Operating System
Tanzania fintech compliance in 2026 operates as a risk-based system combining Bank of Tanzania supervision, AML regulations, FIU reporting, and identity verification infrastructure. Effective implementation requires unified control across onboarding, monitoring, and escalation workflows.
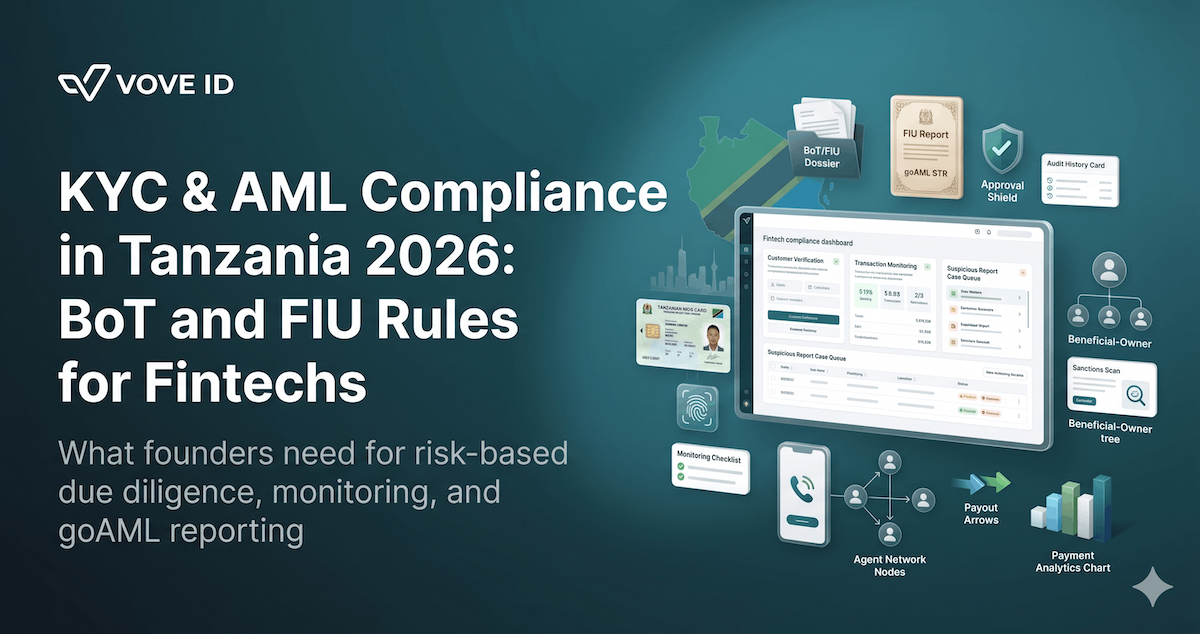
Tanzania compliance in 2026 is not defined by individual controls like KYC or transaction monitoring in isolation. It is defined by how these controls operate together as a single system that can withstand Bank of Tanzania supervision and Financial Intelligence Unit scrutiny.
Unlike standalone KYC or AML processes, compliance in Tanzania is enforced as a lifecycle requirement — from onboarding through transaction activity to reporting and audit.
That matters more now because the market is scaling fast.
Bank of Tanzania's 2024 National Payment System Annual Report shows active mobile money subscriptions reaching 63.21 million, with over 1.4 million agents. At this scale, weak controls do not remain hidden. Gaps between onboarding, monitoring, and reporting become visible quickly under regulatory review.
For fintechs operating wallets, payment platforms, lending products, payroll flows, or merchant services, compliance must function as an integrated operating system rather than a launch checklist.
The Tanzania compliance system in practice
For most fintech teams, compliance is shaped by four interconnected layers that operate continuously rather than independently.
1. Supervisory control environment (Bank of Tanzania)
The Bank of Tanzania regulates and supervises payment systems under the National Payment Systems Act 2015 and related regulations, including Electronic Money Regulations 2015 and Payment Systems Licensing and Approval Regulations 2015.
In practice, BoT supervision extends beyond licensing. It covers:
- how funds move through the system
- how agents are controlled and monitored
- how customer funds are safeguarded
- how transaction data is recorded and retrievable
This means compliance is not a “legal layer” sitting outside the product. It is embedded into system design.
For fintech teams, the key operational implication is that payment infrastructure decisions (wallet design, settlement logic, agent flows) are already part of the compliance perimeter.
2. Risk-based compliance framework (AML Regulations 2022)
The Anti-Money Laundering Regulations, 2022 define how compliance must function in practice.
The core principle is risk-based control application.
This means:
- not all customers are treated equally
- verification depth depends on risk level
- monitoring intensity adapts to behavior
- controls evolve during the customer lifecycle
Risk categories typically include:
- low-risk retail users
- standard-risk business customers
- high-risk cross-border or cash-intensive entities
- politically exposed persons or complex structures
Each category requires a different level of due diligence, monitoring, and escalation logic.
This is where many fintechs misinterpret compliance: they implement KYC as a one-time step, instead of a dynamic system that adjusts over time.
3. Reporting and escalation layer (Financial Intelligence Unit)
The Financial Intelligence Unit (FIU) is responsible for receiving and analyzing suspicious transaction reports.
The operational requirement is strict:
- suspicious activity must be escalated internally
- cases must be reviewed and documented
- reports must be submitted within 24 working hours once suspicion is confirmed
This creates a hard constraint: compliance cannot rely on manual coordination between teams or tools.
A functional system must include:
- clear alert thresholds
- defined case ownership
- structured investigation workflows
- automated documentation of decisions
Without this, reporting becomes reactive and inconsistent under scale.
4. Identity infrastructure layer (NIDA and verification systems)
Tanzania’s identity ecosystem increasingly relies on the National Identification Authority (NIDA), which provides verification services for organizations integrating identity validation.
This creates a hybrid model:
- external identity verification (NIN or national ID systems)
- internal fraud and risk controls
- continuous reassessment of identity confidence
The important point is that identity verification is not fully internal anymore. It depends partially on national infrastructure reliability and integration quality.
For fintechs, this introduces a dependency layer that must be designed into onboarding and monitoring flows.
Agent networks and systemic risk layer
One of the most overlooked parts of Tanzania’s compliance environment is the agent-based financial ecosystem.
With over 1.4 million agents, the system introduces structural risk factors:
- inconsistent agent behavior
- variable KYC enforcement at agent level
- cash-handling exposure
- regional disparities in verification quality
From a compliance perspective, agents are not just distribution channels — they are risk nodes.
This requires:
- agent-level transaction monitoring
- behavioral anomaly detection across regions
- periodic agent risk scoring
- limits on transaction velocity and exposure
Without this layer, even strong KYC at onboarding becomes insufficient.
Where fintech compliance systems break
Most compliance failures in Tanzania come from system fragmentation rather than missing controls.
1. Onboarding and monitoring are disconnected
Customer identity data is collected but not reused in behavioral analysis.
2. Agent and customer risk are treated separately
Agent activity is monitored independently from end-user behavior.
3. Reporting is manual
Case escalation depends on human coordination rather than structured workflows.
4. Audit trails are incomplete
Data is distributed across multiple systems and cannot be reconstructed efficiently.
What a functional compliance system looks like
A working Tanzania compliance architecture connects all layers into a single operational loop:
- onboarding (identity + business verification)
- risk scoring and segmentation
- transaction monitoring
- agent and network monitoring
- escalation and FIU reporting
- long-term record retention
The key shift is from static controls to continuous compliance execution.
In this model:
- onboarding data feeds real-time monitoring
- agent activity influences customer risk
- alerts automatically generate structured case files
- reporting is derived from existing system data, not reconstructed manually
Platforms like VOVE ID enable this model by connecting identity verification, screening, monitoring triggers, and case management into a unified workflow layer.
Product-specific compliance considerations
Different fintech products in Tanzania require different control emphasis.
Wallets and mobile money
- velocity monitoring
- cash-in/cash-out patterns
- agent dependency risk
- peer-to-peer clustering
Payroll and salary distribution systems
- employer funding consistency
- payout distribution anomalies
- beneficiary concentration patterns
Lending platforms
- borrower identity consistency
- repayment behavior deviations
- synthetic identity detection
Merchant and aggregator platforms
- settlement anomalies
- merchant lifecycle monitoring
- cross-merchant pattern detection
Operational compliance maturity stages
Most fintechs evolve through predictable stages:
Stage 1: Static onboarding
KYC exists but is disconnected from product behavior.
Stage 2: Basic monitoring
Transaction flags exist but are not integrated with onboarding data.
Stage 3: Partial integration
Some linking between identity and transactions.
Stage 4: System-level compliance
Onboarding, monitoring, and reporting operate as a unified system.
Tanzania’s regulatory environment accelerates the need to reach Stage 4 earlier than in many markets due to mobile money scale and FIU enforcement expectations.
Tanzania compliance checklist for fintech founders
Before scaling operations, teams should validate:
- Is your BoT licensing scope fully aligned with product functionality?
- Are onboarding and transaction systems connected at data level?
- Does risk scoring change based on customer and agent behavior?
- Can alerts escalate into FIU-ready reports within 24 hours?
- Is agent activity included in compliance monitoring logic?
- Can audit data be reconstructed without manual intervention?
- Are identity systems integrated with national verification infrastructure?
- Does compliance scale with transaction volume rather than manual effort?
Conclusion
Compliance in Tanzania in 2026 is not a set of isolated requirements. It is a system-level discipline built around risk-based controls, supervisory oversight, identity infrastructure integration, and real-time transaction monitoring.
Fintechs that scale successfully in this environment are not those with the simplest onboarding flows. They are those that can demonstrate that compliance operates continuously across customers, agents, and transactions — with full traceability and regulatory alignment.
Explore how integrated compliance workflows can be implemented with VOVE ID.