Remittance Corridors EU → Africa: The Compliance Gap Most APIs Ignore
Most EU-to-Africa remittance APIs solve movement before they solve reconciliation. The corridor doesn't break at the payment rail — it breaks where the sender record, beneficiary data, and payout-side identity requirements stop agreeing.
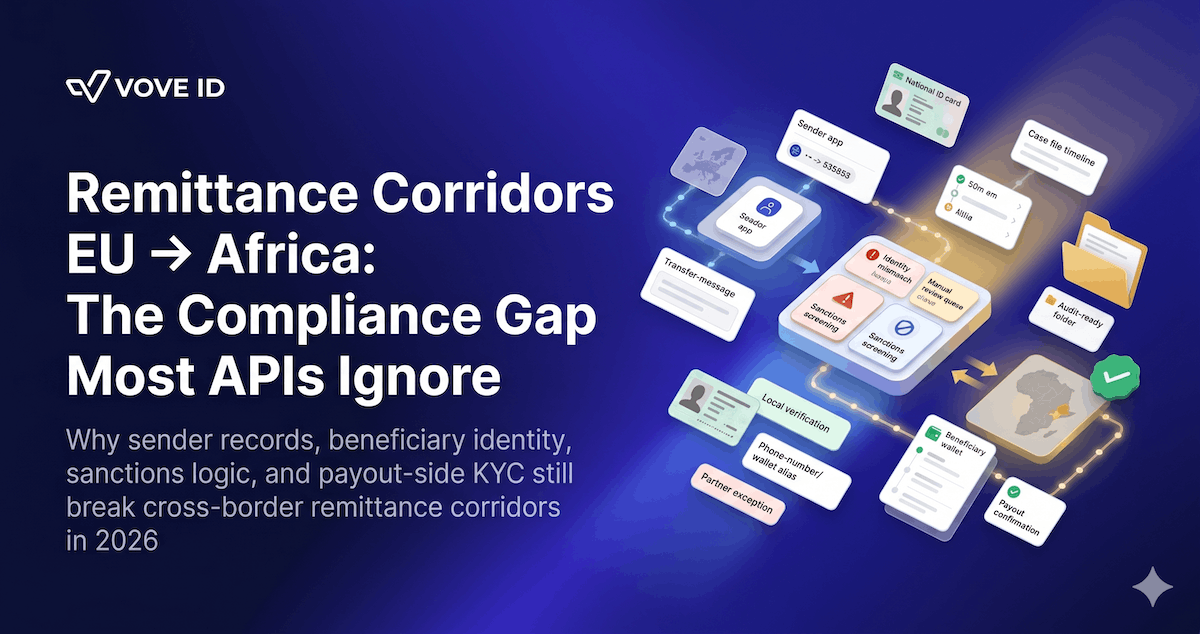
Most remittance APIs solve movement before they solve reconciliation. In 2026, the hardest part of an EU-to-Africa corridor is not sending the payment instruction. It is making the sender record, beneficiary record, sanctions logic, and payout-side identity requirements agree before the transfer hits an exception queue.
What compliance gap do most EU-to-Africa remittance APIs ignore?
They ignore the identity and record-matching gap between the EU sending side and the receiving-side payout environment. The EU provider may have a valid sender file and a compliant payment message, but the corridor still breaks if beneficiary data, local KYC rules, sanctions screening, and payout-partner records do not reconcile in one operational flow.
VOVE ID helps remittance and cross-border fintech teams run compliance in corridors where the European side is structured and the receiving side is fragmented. On paper, the API moves money and the regulated entity keeps its AML controls.
In practice, the corridor fails in the gap between those two things.
Regulatory baseline: what the EU side already requires
The EU side of the corridor is not vague in 2026.
Regulation (EU) 2023/1113 has applied since 30 December 2024. It requires information on payers and payees to accompany transfers of funds and puts traceability obligations around those transfers inside a clearer EU framework.
That sounds technical.
In practice, it means the sender-side provider is expected to know who is sending, who is receiving, what identifying information travels with the payment, and how that information can be retrieved and reviewed later.
The international direction is also getting stricter, not looser.
On 18 June 2025, FATF updated Recommendation 16 on payment transparency. FATF said the changes clarify responsibilities in the payment chain and improve transparency for cross-border payments over USD/EUR 1,000. Formal compliance with the revised standard is measured from 2030, but the supervisory signal is immediate: payment data quality and transfer-message integrity are now core AML issues.
This means one thing: a remittance provider cannot treat corridor data quality as a partner-side nuisance.
Where the corridor actually breaks
Most teams think first about the sender.
That is reasonable. The sender is onboarded by the EU institution. The KYC file is stronger. The sanctions logic is closer. The transaction begins there.
The weaker side of the corridor is usually the beneficiary record.
Not because the receiving partner is careless, but because the data environment is different. Name order changes. Local ID formats vary. Mobile wallet records are built for payout, not for full cross-border audit logic. Address data is inconsistent. A payout partner may accept a local convention that does not map neatly to the sender-side compliance record.
So the payment looks complete on paper and incomplete in practice.
Receiving-side compliance: why local rules still matter
The Africa side of the corridor is not one legal environment.
That is the first mistake teams make.
A provider can say it serves "Africa" and still operate into very different identity regimes, payout models, and regulatory expectations. In West Africa alone, the BCEAO issued Instruction n°003-03-2025 on customer identification, identity verification, and KYC by financial institutions. That matters because payout, wallet, and transfer participants still have to anchor customer records in local identity rules.
This does not mean every corridor needs a new stack.
It does mean every corridor needs a corridor-aware identity layer. If the EU side sends a clean sender record into a receiving environment that uses different naming conventions, different acceptable identifiers, or different review thresholds, the API alone does not close the compliance problem.
A realistic corridor failure: when the payment clears and the beneficiary does not
A Polish-licensed remittance startup pays out to Senegal through a local wallet partner.
The startup has:
- a verified sender record from EU onboarding
- a valid payer message
- sanctions screening on sender and beneficiary name
- a wallet number for the recipient
Then the inconsistencies appear.
The sender entered the beneficiary's full name in one order. The payout partner stores the name in another. One surname is truncated on the wallet record. The sanctions engine returns a weak match because the beneficiary name is common. The local review team wants an additional identifier before release, but that field was never collected in the sender app.
So operations intervenes manually.
The transfer is paused. The customer asks support why funds did not arrive. The compliance team reviews screenshots from two systems and one partner email thread. The payment may still complete, but the case record now depends on reconstruction.
This is not a rails failure.
It is a reconciliation failure.
Why most APIs miss it
Most remittance APIs are built to optimize:
- route selection
- payout speed
- fee calculation
- integration effort
Those things matter.
But they do not solve the core compliance problem if the record is split across the sender institution, the messaging layer, the sanctions engine, the payout partner, and the manual-review queue.
That is why teams feel friction most sharply in three places:
- beneficiary mismatches that were predictable upstream
- sanctions reviews with low-confidence identity data
- audit requests that need one end-to-end corridor file and get five partial ones
The issue is structural, not cosmetic.
How VOVE ID approaches this: one corridor record, not two
VOVE ID helps remittance teams connect sender identity, beneficiary identity, screening, monitoring, and case handling in one corridor-aware workflow.
That matters because the transfer is only safe when both ends of the corridor describe the same people in a way the compliance team can defend.
VOVE ID closes that gap by helping teams:
- normalize sender and beneficiary identity data before payout release
- attach sanctions decisions to the exact transfer and record version reviewed
- keep partner-side exceptions inside one case trail
- score corridor-specific risk patterns instead of treating all payouts the same
- store one audit record for onboarding, transfer review, escalation, and outcome
The result is not only fewer payout exceptions.
It is a corridor that can be explained after the fact without relying on inbox archaeology.
Practical corridor-compliance checklist
Sender
- Collect the sender fields your payment message and receiving partner both need.
- Tie expected corridor behavior to the sender risk profile at onboarding.
- Re-screen sender records when corridor usage changes materially.
Beneficiary
- Normalize beneficiary names, identifiers, and wallet or account data before release.
- Capture corridor-specific fields early instead of waiting for a partner rejection.
- Track recurring mismatch patterns by corridor and payout partner.
Monitoring
- Review sanctions hits against the exact beneficiary record used for payout.
- Flag repeated manual interventions as a monitoring issue, not only an ops issue.
- Separate corridor-level risk from generic transaction-volume risk.
Reconciliation
- Keep one case trail for transfer message, partner exception, review notes, and release decision.
- Store the final beneficiary record and the pre-normalized input together.
- Test whether one file can explain the transfer from sender onboarding to payout completion.
FAQ
What compliance gap do remittance APIs usually miss?
They usually miss the reconciliation gap between the sender-side compliance record and the receiving-side beneficiary record. A transfer can be valid in the sender system and still fail operationally if the payout-side identity data does not match cleanly.
Why are EU-to-Africa corridors harder than they look?
Because the corridor joins different identity conventions, payout models, local KYC expectations, and partner data structures. The money can move faster than the compliance record can stay consistent.
Is this mainly a sanctions problem?
No. Sanctions are part of it, but the deeper issue is record quality. Weak beneficiary data, inconsistent identifiers, and partner-side exceptions create the conditions that make sanctions review and audit reconstruction harder.
What should remittance teams build first?
They should build one corridor-aware record that connects sender data, beneficiary data, screening results, partner exceptions, and final release decisions. That is what keeps the case defensible after the transfer leaves the sender platform.
Conclusion
EU-to-Africa remittance compliance is not only a payment problem. It is a record-consistency problem across two ends of the corridor.
Teams that solve only for movement keep rediscovering the same failure downstream: the sender file is compliant, the payment message is valid, and the payout still stalls because the corridor identity layer was never designed properly.
Movement, screening, and reconciliation are one workflow.
Want to see how VOVE ID closes EU-to-Africa remittance corridors with one identity, screening, and case-management layer? Talk to the team.